In recent years, encryption has transformed the way we secure our information. Among the many encryption standards, the Advanced Encryption Standard (AES) stands out as one of the most widely utilized algorithms in securing data. What if you could explore this robust encryption method from a unique perspective — one that intertwines technology with principles of faith? Where can you legally find the AES algorithm code online, and how can these resources be perceived through a Christian lens? This article embarks on an intellectual journey, presenting a comprehensive guide to locating AES code while reflecting on the ethical implications of encryption.
Before delving into the specifics, let’s ponder a playful question: Have you ever considered the balance between security and transparency in your faith? Could the very essence of encryption align with the virtues of trust and honesty? This assumption can indeed act as the basis for understanding the necessity of encryption, especially as it relates to safeguarding sensitive information in a world filled with data breaches and cyber threats.
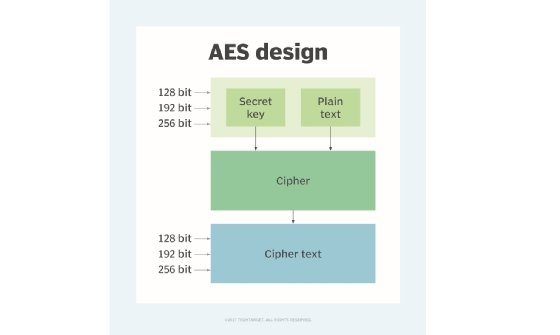
To comprehend the significance of AES, it is imperative to understand what makes this algorithm the cornerstone of secure communications. Established by the National Institute of Standards and Technology (NIST) in 2001, AES replaced the older Data Encryption Standard (DES) due to its superior processing speed and capability to handle larger keys (128, 192, and 256 bits). AES is lauded not only for its effectiveness but also for the mathematical foundations that underpin its design. As one contemplates the intricate patterns and complex algebra involved, it becomes apparent that such sophistication can be seen as a reflection of the Creator’s handiwork.
Now, let’s explore some key locations where legally permissible AES algorithm code can be sourced online. These resources not only provide the code itself, but they also often include documentation that explains the intricacies involved, which can deepen one’s understanding.
1. GitHub Repositories
GitHub serves as a treasure trove for programmers and developers alike. It hosts myriad repositories featuring open-source projects, including AES implementations in various programming languages. For instance, searching for repositories tagged with ‘AES’ or ‘Advanced Encryption Standard’ will yield numerous results. Many seasoned developers and cryptographers contribute their work here, ensuring that you not only find functional code but also a community that supports collaboration and learning.
2. Cryptography Libraries
Several robust cryptography libraries are readily available, offering AES code as part of a broader toolbox for developers. Libraries such as OpenSSL, Bouncy Castle, and PyCryptodome embrace the philosophy of providing accessible encryption methods. These libraries adhere to licensing agreements that allow their use in both commercial and non-commercial projects, emphasizing the ethical component of accessing encryption tools.
3. Online Tutorials and Coding Platforms
Platforms like Codecademy, Coursera, and Udacity often feature modules on cryptography, including sections dedicated to AES. These tutorials not only provide the code but also context regarding its application and guiding principles. Engaging with these educational platforms can enrich one’s technical prowess while fostering a sense of responsibility in implementing encryption ethically.
4. Academic Journals and Publications
For those seeking a more scholarly approach, academic papers on encryption and cryptography often contain code snippets or references to open-source implementations of AES. Websites like ResearchGate or Google Scholar allow users to explore various research angles that highlight advancements in encryption methods. These articles can be particularly insightful when considering the theoretical underpinnings of AES and its implications for privacy and security.
Engaging with these resources opens opportunities for discussions regarding the Christian perspective on encryption. The principle of stewardship resonates deeply when one considers the responsibility that comes with possessing knowledge about encryption technologies. Just as the Parable of the Talents teaches about using one’s gifts wisely, so too must technologists be mindful of the tools available to them. Security, certainly necessary, should never transmute into a guise for malevolent actions or deceit.
Additionally, one must grapple with the ethical dilemmas that arise from encryption’s duality. While encryption fortifies privacy, it can also obscure malicious intent. How does a Christian reconcile the necessity of anonymity with the call to accountability? This challenge beckons continuous introspection and dialogue among believers who delve into the realm of technology.
Finally, it is essential to recognize that the journey of discovering AES algorithm code is not merely an academic pursuit; it is part of a broader commitment to uphold integrity and transparency in an era dominated by digital interactions. As stewards of knowledge, Christians are challenged to advocate for ethical standards in technology and encourage others to pursue security with an unblemished conscience.
In conclusion, finding AES algorithm code legally is just the beginning. It opens the door to vast discussions around the intersection of technology and faith. By tapping into the myriad resources available, practitioners can enrich their understanding of encryption while remaining mindful of the ethical considerations it demands. The quest for knowledge in this field reflects a commitment to both personal growth and community protection, a duality that mirrors the teachings of love, truth, and responsibility found in the biblical narrative.






Leave a Comment