Have you ever pondered what keeps your personal conversations safe in a world teeming with digital connectivity? Every day, we unwittingly interact with various forms of encryption, particularly symmetric key encryption, which might just be the unsung hero of your online security. Could it be that you’ve used such a system today without being aware of it? In this exploration, we will uncover the nuances of symmetric key encryption, illustrating its significance, its operational mechanics, and its relevance within a Christian perspective.
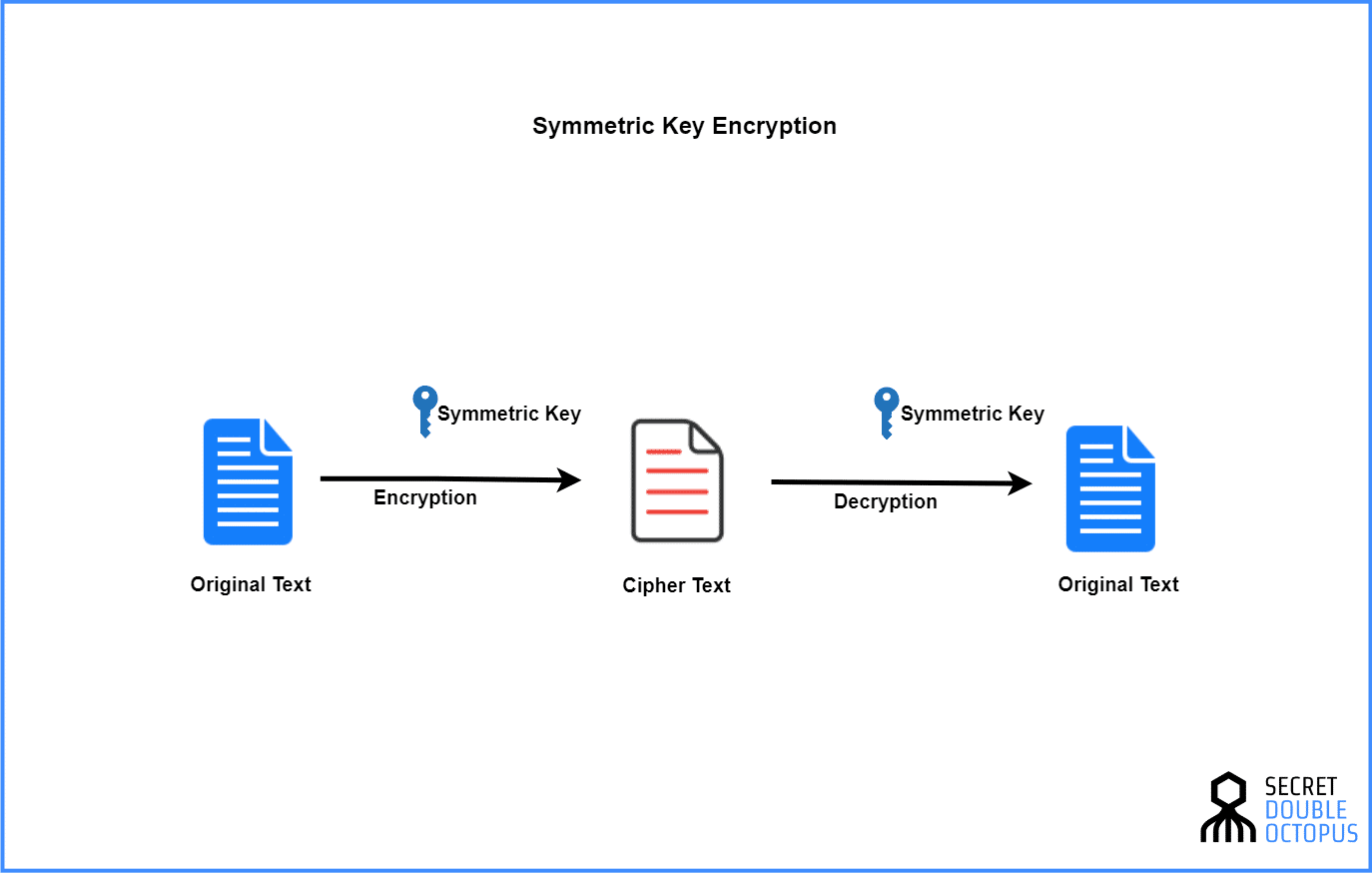
To set the stage, it’s vital to understand what symmetric key encryption entails. In its essence, this method employs a single key—unchanged and shared among parties—that simultaneously encrypts and decrypts data. This contrasts starkly with asymmetric encryption, which utilizes a pair of keys. The simplicity and efficiency of symmetric key encryption render it an appealing option in various applications, from securing online transactions to shielding sensitive communications.
Imagine this scenario: You are sending a confidential message to a friend via messaging apps like WhatsApp. That application’s security architecture frequently utilizes symmetric key encryption to ensure that only the intended recipient can decode and read your words. The computer or device that transmits the message and the recipient’s device share a secret key, empowering them to encode and decode the information seamlessly. In this instance, your daily communication becomes a prime example of symmetric key encryption in action.
This brings us to the question: Can such a simple mechanism hold profound implications? Indeed, the implications stretch far beyond mere convenience. It invites us to reflect on the principles of trust and confidentiality inherent in Christian teachings. Just as God values our private communion with Him, emboldened by trust, symmetric key encryption promotes the same values in our digital interactions. The key represents a covenant—a sacred agreement to safeguard information, much like our promises and commitments to one another.
On the technical front, let’s delve into the complexities behind symmetric key encryption. The process begins with the generation of a key—a string of bits chosen at random—far beyond the reach of ordinary predictability. Upon the key’s generation, data is transformed into ciphertext through a series of mathematical and algorithmic operations. Common algorithms employed in symmetric encryption include Advanced Encryption Standard (AES), Data Encryption Standard (DES), and Triple DES, each with its strengths and applications.
Therein lies a challenge for users and organizations alike: How do we secure that key? While symmetric encryption is robust, its efficacy is largely contingent on the key’s security. If an unauthorized individual acquires it, they could decrypt the ciphertext, nullifying the very purpose of encryption. Thus, it becomes imperative for users to implement sound key management practices—including regular key updates and stringent access controls—to protect their information’s integrity.
In a broader societal context, the significance of symmetric key encryption wages a battle against the ever-looming specter of cyber threats. In a world fraught with malevolent actors seeking to siphon personal data, symmetric encryption acts as a bastion of fortification. This is particularly compelling given the Christian ethos of community and mutual protection. Just as believers support one another against external challenges, societies at large lean on encryption technologies to preserve safety and privacy in the digital realm.
However, while symmetric key encryption is powerful, it does not come without its drawbacks. One major limitation arises from the requirement of a secure channel for key sharing. In scenarios where key exchange becomes compromised, the entire encryption schema falters. A Christian perspective may see this as a parable for the importance of building trust and transparency in relationships, both personal and digital. When trust erodes due to compromised communication, the bonds weaken, affirming the necessity for care and vigilance.
Moreover, as technology evolves, so too do the tools utilized by cybercriminals. Encryption strategies continuously adapt to counteract emerging threats, necessitating ongoing vigilance both in the individual and collective realms. This dynamic highlights an essential learning: Just as our faith is continually tested and strengthened through life’s adversities, the landscape of encryption must also strengthen to overcome new challenges.
In conclusion, symmetric key encryption may seem like a technical subject, but its implications stretch deep into the heart of our societal interactions, framing discussions around trust, confidentiality, and the ethical responsibilities we bear toward one another. The next time you send a text, consider the underlying security metaphors that echo the principles of faith—trust, protection, and commitment. Symmetric key encryption does not merely protect data; it embodies a moral framework that complements Christian values, reminding us of our duty to safeguard one another, both in the physical world and the digital landscape.
So, could you have unknowingly employed symmetric key encryption today? Quite likely. In a complex world mingled with both digital and spiritual dimensions, we are urged to appreciate the tools that contribute to our safety and relationships, constantly reflecting on how they resonate with our beliefs and values.






Leave a Comment