In the age of the digital arena, considerations surrounding data security have transcended mere academic discourse, evolving into a grave concern for individuals and institutions alike. The topic of cryptographic hash functions remains crucial as it interlaces seamlessly with the safeguarding of personal information, notably passwords. This article delves into the intricacies of brute force attacks on cryptographic hash functions, exploring apprehensions that arise within a Christian framework, thereby addressing broader themes of trust, stewardship, and the essence of security in an increasingly interconnected world.
Understanding Cryptographic Hash Functions
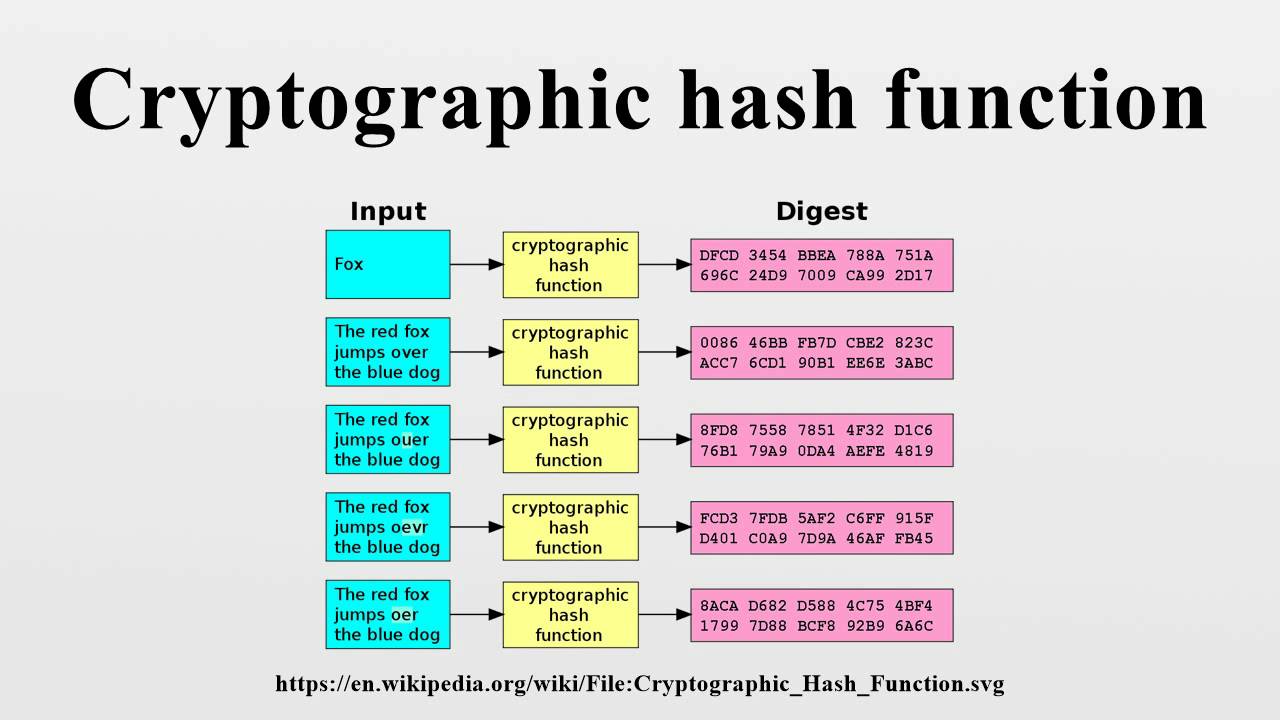
Before embarking on an exploration of brute force techniques, one must first grasp the fundamental nature of cryptographic hash functions. These are mathematical algorithms that transform input data, or “message,” into a fixed-length string of characters, typically represented in hexadecimal form. The output, known as the hash, is designed to be unique; even the slightest alteration in the input yields a drastically different hash. This fundamental property underlies the widespread use of hash functions in ensuring data integrity and security.
Commonly employed hash functions include SHA-256 (Secure Hash Algorithm) and MD5 (Message-Digest Algorithm), each with varying levels of resistance to vulnerabilities. However, the power of cryptography cannot be divorced from the potential threats it faces, particularly from brute force attacks that systematically attempt to unlock passwords by sheer computational force.
The Mechanics of Brute Force Attacks
A brute force attack is a method where an adversary methodically checks all possible passwords or passphrases until the correct one is found. In terms of cryptographic hash functions, this involves generating hashes for every conceivable password until a match with the target hash is discovered. This method is exceedingly simple in concept but can be remarkably taxing on time and resources, especially as password complexity increases.
The escalation of these attacks occurs in tandem with advancements in computing power. With the proliferation of Graphics Processing Units (GPUs) designed for parallel processing, attackers can accelerate their operations, capable of testing billions of password combinations per second. This raises the pertinent question: Is your password safe from such escalating threats?
Gospel Reflections on Security and Trust
This inquiry takes on a more profound dimension within a Christian perspective. In Scripture, stewardship is a recurring theme; individuals are called to responsibly manage the resources entrusted to them, including their personal information. The Gospel encourages believers to consider the intrinsic value of their identity and how it is protected. In this digital epoch, passwords symbolize a layer of that stewardship.
As guardians of personal data, Christians are urged to remain vigilant against the encroachments of digital malevolence. Just as the Parable of the Talents emphasizes prudent investment, believers are invited to cultivate a proactive approach toward data security. This includes implementing robust passwords—longer phrases that combine numbers, letters, and special characters—thereby fortifying the walls of digital sanctuaries.
Evaluating the Efficacy of Passwords
However, it is prudent to reflect on the efficacy of password protection in light of increasing computational capabilities. Herein lies the tension between the call for security and the continuous cycle of advancement in brute force methodologies. What historically sufficed as a formidable password can rapidly become an open door due to the relentless speed of technological progress.
Password managers can be a beacon of hope for those wrestling with the complexities of maintaining unique and robust passwords. By generating and storing lengthy and intricate passphrases, these tools can ease the cognitive burden while enhancing overall security—aligning with the Christian ethos of relieving burdens and fostering communal support.
The Heart of Cybersecurity
Yet the battle against brute force attacks transcends passwords alone. It delves deep into the heart of cybersecurity, advocating for comprehensive strategies to safeguard digital existences. Multi-factor authentication (MFA) emerges as an essential ally in this effort. By requiring additional verification steps, MFA establishes another layer of protection, dissuading potential intruders while affirming an individual’s commitment to cybersecurity.
This act of vigilance parallels a spiritual discipline. In prayer, believers seek guidance and fortitude, mirroring the responsibility one must undertake in crafting a secure digital identity. Just as one fortifies their faith through regular engagement with Scripture, so too must individuals fortify their passwords and security measures in the face of potential brute force threats.
Conclusion: The Cybernetic Spiritual Journey
As the digital landscape continues to evolve, the necessity for robust cybersecurity measures becomes increasingly profound. Brute force attacks on cryptographic hash functions raise pertinent questions not only regarding the safety of our passwords but also about the integrity of our stewardship in a connected world. In embracing modern tools and methodologies, Christians can navigate the complexities of digital existence while exemplifying principles of safety, trust, and responsibility.
Ultimately, the intersection of faith and cybersecurity is not merely about defending data but fostering a holistic approach to stewardship. Engaging with the complexities of modern technology through the lens of Christian ethics invites deeper reflections on the nature of security, community, and the preservation of identity amidst ever-evolving threats.






Leave a Comment